
Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
In this era of Cyber-espionage and breaches, Data security is critical for the positive development of the society . The most prevalent medium of securing data is through various techniques preventing third parties reading the information which called ciphers , which come under the broader umbrella of cryptography.This article is based on exactly on the understanding of what are ciphers. Before we go into the intricacies of the various kinds of cipher ,their uses and working ; we need to exactly does a cipher mean , what is cryptography, cryptanalysis and how is the notion of hiding or securing data using algorithms and texts was born.
History of Cryptography,Cryptanalysis and Ciphers
Cryptography - past and present
Cryptography is the practice and study of techniques for secure communication in the presence of third parties. All the more by and large, cryptography is tied in with building and investigating conventions that keep outsiders or people in general from perusing private messages; different angles in data security, for example, information secrecy, information uprightness, validation, and non-renouncement are integral to current cryptography.
The first use of the term cryptograph dates back to the 19th century originating from The Gold-Bug, a novel by Edgar Allan Poe. Prior to the Modern period, cryptography zeroed in on transformation of messages from a fathomable structure into an inconceivable one known as encryption and back again at the opposite end known as decryption and making it incomprehensible by interceptors or snoops without key information .
Present day cryptography exists at the crux of the controls of arithmetic, software engineering, electrical designing, correspondence science, and physical science. Uses of cryptography incorporate electronic business, chip-based installment cards, advanced monetary standards, PC passwords, and military interchanges.
Ciphers
The word "cipher" (minority spelling "cypher") in former times meant "zero" and had the same origin: Middle French as cifre and Medieval Latin as cifra, from the Arabic صفر sifr = zero.
In cryptography, a cipher is a calculation for performing scrambling(encryption) or unscrambling(decryption) data through a progression of very much characterized advances that can be followed as a methodology. In common usage , a code is now considered as same as a cipher as they do generate the same output albiet through different methods. We will differentiate between the two later below.
The activity of a cipher typically relies upon a bit of helper data, called a key. The encoding technique is shifted relying upon the key, which changes the activity of the calculation. A key must be chosen before utilizing a cipher to scramble a message. Without information on the key, it ought to be incredibly troublesome, if certainly feasible, to unscramble the subsequent cipher-text into decipherable plain-text.
Cryptanalysis
Another term which usually comes up when talking about cryptography and ciphers is cryptanalysis. Many people make the false assumption that cryptography and cryptanalysis are the same. Lets remove that mis-conception.
Cryptanalysis refers to the study or practice to understand information systems to extract hidden data aspects of the said system. it involves mathematical analysis of the system along with non-mathematical aspects which help in understanding the system better and to crack the data hidden.
it is synonymous with ciphers as ciphers tend to be the most easily accessible part of any information system bent on hiding its data, which makes it an important part in cryptanalysis.Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past to the mathematically advanced computerized schemes of the present.
Hence, in easier terms , both ciphers and cryptanalysis come under the broad umbrella of cryptography and and integral parts of it.
How are Ciphers different from Codes
| text | ciphers | codes |
|---|---|---|
| output | ciphers generally substitute the same number of characters as are input | Codes generally substitute different length strings of character in the output |
| working | Ciphers, on the other hand, work at a lower level: the level of individual letters, small groups of letters, or, in modern schemes, individual bits and blocks of bits. | Codes operated by substituting according to a large codebook which linked a random string of characters or numbers to a word or phrase. |
| utility | easier to maintain due to use of algorithms | cumbersome due to maintenance of a large code book |
| vulnerability to cryptanalysis | less compared to codes as it tends to alternate each character of the input rather than words making sense | very vulnerable as it is based for making only words compact rather than complete hiding of data |
Classification of ciphers based on era
Now that we have understood the basic terminologies related to ciphers , we can move forward on the classifications and intricacies of the various kinds of ciphers.Ciphers are classified into two types based on the time period of usage-
- Classic Ciphers
- Modern ciphers
Classic Ciphers and its classifications
In cryptography, a classical cipher is a kind of cipher that was utilized verifiably yet generally, has fallen into neglect. The classical ciphers were developed pre-PC up until around the 1950's. As opposed to current cryptographic calculations, most traditional ciphers can be basically figured and illuminated by hand. Notwithstanding, they are additionally typically easy to break with present day innovation. The term incorporates the straightforward frameworks utilized since Greek and Roman occasions, the intricate Renaissance ciphers, World War II cryptography, for example, the Enigma machine.
Classical ciphers are often divided into -
- Substitution ciphers
- Transposition ciphers
Substitution ciphers and its classification
In cryptography, a substitution cipher is a technique for encoding by which units of plain-text are supplanted with cipher-text, as indicated by a fixed framework; the "units" might be single letters (the most well-known), sets of letters, trios of letters, blends of the above mentioned, etc. The beneficiary translates the content by playing out the converse replacement.
Substitution ciphers can be contrasted with transposition ciphers . In an transposition ciphers, the units of the plain-text are improved in an alternate and typically very complex format, however the units themselves are left unaltered. Paradoxically, in a substitution cipher , the units of the plain-text are held in a similar arrangement in the cipher-text, yet the units themselves are adjusted.
Substitution ciphers can be classed into various types which we will discuss below.
- Mono-alphabetic or simple substitution ciphers
Monoalphabetic cipher is a substitution cipher in which for a given key, the code letter set for each plain letters in order is fixed all through the encryption cycle. For instance, if 'An' is scrambled as 'D', for quite a few event in that plaintext, 'A' will consistently get encoded to 'D'.
Substitution of single letters independently — basic replacement — can be exhibited by working out the letters in order in some request to speak to the replacement. This is named a substitution alphabet set. The code letters in order might be moved or switched or mixed in a more perplexing manner, in which case it is known as a blended letter set or unsettled letters in order.Most common examples are Caesar Cipher and Atbash cipher.
Working of Caesar cipher
To pass an encoded message starting with one individual then onto the next, it is first important that the two players have the 'key' for the code, so the sender may scramble it and the collector may unscramble it. For the Caesar cipher, the key is the quantity of characters to move the code letters in order.
First we decipher the entirety of our characters to numbers, 'a'=0, 'b'=1, 'c'=2, ... , 'z'=25. We would now be able to speak to the Caesar cipher encryption work, e(x), where x is the character we are encrypting, as:
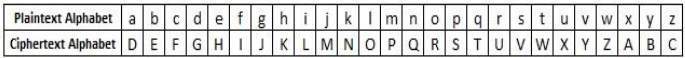
Where k is the key (the move) applied to each letter. Subsequent to applying this capacity the outcome is a number which should then be made an interpretation of back into a letter. The decrypting capacity is :
- Poly-alphabetic ciphers
Poly-alphabetic Substitution cipher was presented by Leon Battista in the year 1568, and its unmistakable models are Vigenère code and Beaufort figure.
We utilize various one-character keys, each key scrambles one plain-text character. This first key scrambles the primary plain-text character, the second the key encode the second plain-text character, etc, all things considered, keys are utilized then they are reused. In the event that 50 one-letter keys, each 50th character in the plain content would be put with a similar key and this number (for our situation, 50) is time of the code.
The central issues of the poly-alphabetic substitution figure are the accompanying:
- It utilizes a lot of related mono-alphabetic replacement rules.
- The rule used for changes dictated by the key it employs.
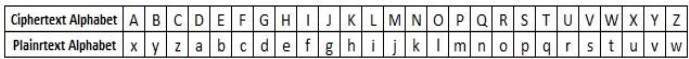
Working of Vigenere Cipher
- The 'key' for a vigenere cipher is a key word. e.g. 'FORTIFICATION' . The Vigenere Cipher uses the following tableau (the 'tabula recta') to encipher the plaintext:
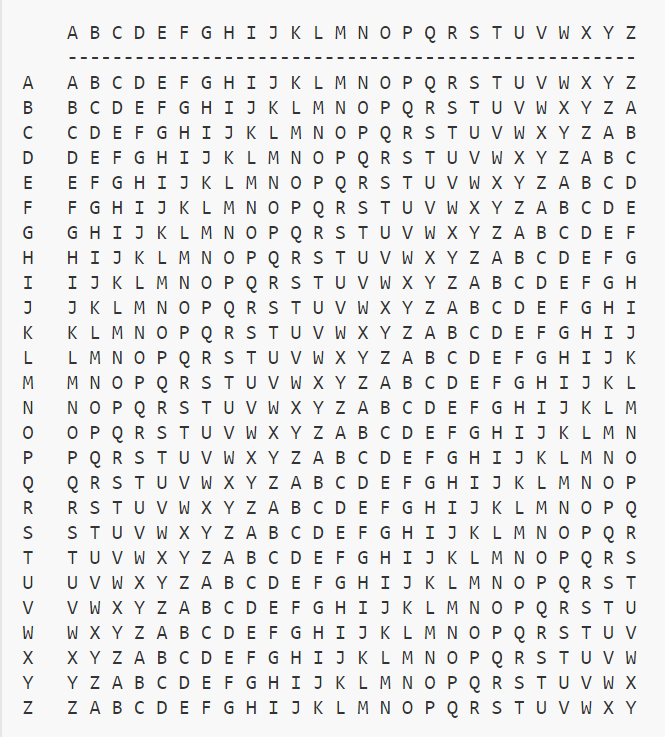
2.To encipher a message, repeat the keywords above.
- Now we take the letter we will be encoding, and find it on the first column on the tableau. Then, we move along the row of the tableau until we come to the column with the keyword at the top, the intersection is our ciphertext character.
Difference between Mono-alphabetic and Poly-alphabetic Ciphers
| Mono-alphabetic Cipher | Poly-alphabetic Cipher |
|---|---|
| each symbol in plain text is mapped to a fixed symbol in cipher text | cipher is based on substitution, using multiple substitution alphabets. |
| Each alphabetic character of plain text is mapped onto a unique alphabetic character of a cipher text. | Each alphabetic character of plain text can be mapped onto ‘m’ alphabetic characters of a cipher text. |
| Cryptanalysis is very easy | Cryptanalysis is comparatively difficult |
3.Homophonic Substitution Cipher
The Homophonic cipher and mono-alphabetic cipher are a lot of the same. Like in plain code substitution we supplant a letter set with a key however in the event of Homophonic Substitution, we map a letter set with a lot of fixed keys (more than one key). For example, A can be supplanted with H, J, O, P and B will supplant with any of the accompanying inspite of A's key set D, I, W, Z and so on.
A very good example of this particular type is Beale cipher.
4.Polygram Substitution Cipher
In Polygram substitution cipher, rather than supplanting one plain-text letters in order we basically supplant a square of the word with another square of a word. Model, 'INCLUDEHELP' will change to 'WDSAEQTGTAI' though 'HELP' will supplant to 'RYCV'. This is genuine that the last four letters are the equivalent yet at the same time unique in the two words.
The principal advantage is that the recurrence circulation is a lot compliment than that of individual letters (however not in reality level in genuine dialects; for instance, 'TH' is substantially more typical than 'XQ' in English). Second, the bigger number of images requires correspondingly more cipher-text to beneficially examine letter frequencies. To substitute sets of letters would take a substitution letters in order 676 images in length .
Good examples of this type are Hill Cipher and Playfair Cipher.
5.Mechanical substitution ciphers
Between around World War I and the boundless accessibility of PCs (for certain administrations this was roughly the 1950s or 1960s; for different associations it was 10 years or all the more later; for people it was no sooner than 1975), mechanical usage of poly-alphabetic substitution ciphers were broadly utilized . These were comparative in that the subbed letter was picked electrically from among the colossal number of potential mixes coming about because of the pivot of a few letter circles. Since at least one of the circles pivoted precisely with each plain-text letter enciphered, the quantity of letter sets utilized was cosmic.
The enigma machine is one of the greatest example of the particular type of cipher.
6.The one-time pad
One type of substitution cipher, the one-time pad, is quite special. It was invented near the end of World War I by Gilbert Vernam and Joseph Mauborgne in the US.
The one-time pad is, much of the time, unfeasible as it necessitates that the key material be as long as the plain-text, really arbitrary, utilized once and just a single time, and kept altogether mystery from all with the exception of the sender and planned beneficiary. At the point when these conditions are disregarded, even possibly, the one-time pad is not, at this point tough.
Transposition ciphers and its examples
In cryptography, a transposition cipher is a technique for encryption by which the positions held by units of plain-text (which are ordinarily characters or gatherings of characters) are moved by a customary framework, so that the cipher-text establishes a stage of the plain-text. That is, the request for the units is changed (the plain-text is reordered). Numerically a bijective capacity is utilized on the characters situations to scramble and a backwards capacity to decode.
Transposition is frequently joined with different strategies, for example, assessment techniques. For instance, a basic substitution cipher joined with a columnar transposition dodges the shortcoming of both. Supplanting high recurrence cipher-text images with high recurrence plain-text letters doesn't uncover pieces of plain-text as a result of the transposition. Anagramming the transposition doesn't work in light of the substitution. The procedure is especially incredible whenever joined with fractionation (see underneath). An impediment is that such ciphers are impressively more difficult and blunder inclined than less complex ciphers.
Transposition is especially viable when utilized with fractionation , that is, a starter stage that partitions each plain-text image into a few cipher-text symbols.When such a fractionated message is rendered, the segments of individual letters become generally isolated in the message. Instances of ciphers that consolidate fractionation and transposition incorporate the bifid cipher, the trifid cipher, the ADFGVX cipher and the VIC cipher.
Other examples of Transposition Ciphers are - Scytale,Rail Fence , Columnar transposition , Double Transposition.
Below are the workings of a few popular transposition ciphers.
Working of Scytale
Scytale was an encryption gadget utilized by the Ancient Greeks and Spartans. It comprised of a polygonal bar or chamber, around which was wrapped a bit of material. The sender would compose the message along the essences of the pole as found in the picture underneath. At the point when the material is taken out from the Scytale, it leaves a strange message going down the strip (for the situation underneath it would peruse "STSF...").
Working of Rail Fence Cipher
To encryption a message utilizing the Rail Fence Cipher, you need to compose your message in crisscross lines over the page, and afterward read off each line. Right off the bat, you have to have a key, which for this cipher is the quantity of lines you will have. You at that point begin composing the letters of the plain-text slantingly down to one side until you arrive at the quantity of lines determined by the key. You at that point ricochet back up slantingly until you hit the principal column once more. This proceeds until the finish of the plain-text.
The decryption cycle for the Rail Fence Cipher includes remaking the askew framework used to encode the message. We begin composing the message, yet leaving a scramble instead of the spaces yet to be involved. Step by step, you can supplant all the runs with the relating letters, and read off the plain-text from the table.We start by making a matrix with the same number of lines as the key seems to be, and the same number of segments as the length of the cipher-text. We at that point place the primary letter in the upper left square, and runs slantingly downwards where the letters will be. At the point when we return to the top line, we place the following letter in the cipher-text. Proceed with like this over the column, and start the following line when you arrive at the end.
Working of Columnar Transposition Cipher
We first pick a keyword for our encryption. We compose the plain-text out in a framework where the quantity of sections is the quantity of letters in the watchword. We at that point title every section with the particular letter from the watchword. We take the letters in the watchword in sequential request, and read down the sections in a specific order. In the event that a letter is rehashed, we do the one that shows up first, at that point the following, etc.
The decryption cycle is fundamentally simpler if nulls have been utilized to cushion out the message in the encryption cycle. Beneath we will discuss how to approach unscrambling a message in both scenarios. Firstly, in the event that nulls have been utilized, at that point you start by working out the watchword and the sequential request of the letters of the catchphrase. You should then separation the length of the cipher-text by the length of the watchword. The response to this is the quantity of columns you have to add to the network. You at that point compose the cipher-text down the primary section until you arrive at the last line. The following letter turns into the primary letter in the subsequent section (by the sequential request of the keyword, etc.
Cryptanalysis of Classic Ciphers
Traditional ciphers are generally very simple to break. A considerable lot of the old style ciphers can be earned back the original investment if the aggressor just knows adequate cipher-text and subsequently they are helpless to a cipher-text-just assault. Some traditional ciphers (e.g., the Caesar cipher) have a little key space. These ciphers can be broken with a beast power assault, that is by just evaluating all keys. Substitution ciphers can have a huge key space, however are regularly powerless to a recurrence investigation, on the grounds that for instance successive letters in the plain-text language compare to visit letters in the cipher-texts. Poly-alphabetic ciphers, for example, the Vigenère cipher forestall a basic recurrence investigation by utilizing numerous substitutions.
Modern ciphers and its classifications
Modern encryption methods can be divided by two criteria: by type of key used, and by type of input data.
On the basis of input data:
- Stream ciphers
- Block Ciphers
On the Basis of key used:
- Asymmetric key algorithms (Public-key cryptography), where two different keys are used for encryption and decryption.
- Symmetric key algorithms (Private-key cryptography), where the same key used for encryption and decryption.
Asymmetric cryptography
Public-key cryptography, or asymmetric cryptography, is a cryptographic framework that utilizations sets of keys: public keys, which might be spread generally, and private keys, which are known distinctly to the proprietor. The age of such keys relies upon cryptographic calculations dependent on numerical issues to deliver single direction capacities. Compelling security just requires keeping the hidden key private; the public key can be straightforwardly circulated without trading off security.
Two of the most popular employments of public key cryptography are:
-
Public key encryption, in which a message is scrambled with a beneficiary's public key. The message can't be unscrambled by any individual who doesn't have the coordinating private key, who is accordingly dared to be the proprietor of that key and the individual related with the public key. This is utilized trying to guarantee privacy.
-
Digital Signatures, in which a message is marked with the sender's private key and can be checked by any individual who approaches the sender's public key. This confirmation demonstrates that the sender approached the private key, and consequently is probably going to be the individual related with the public key. This additionally guarantees the message has not been altered, as a mark is numerically bound to the message it initially was made with, and confirmation will come up short for all intents and purposes some other message, regardless of how like the first message.
Examples of Public-key cryptography
- Diffie–Hellman key exchange protocol
- ElGamal
- RSA encryption algorithm
- Digital Signature Algorithm
Weakness of Public-key cryptography
All open key plans are in principle defenseless to a "savage power key inquiry assault". Much of the time, the work factor can be expanded by essentially picking a more drawn out key. In any case, different calculations may have a lot of lower work factors, making protection from a savage power assault unimportant. Some uncommon and explicit calculations have been created to help in assaulting some open key encryption calculations – both RSA and ElGamal encryption have known assaults that are a lot quicker than the savage power approach.
Another potential security weakness in utilizing asymmetric keys is the chance of a "man-in-the-center" assault, in which the correspondence of public keys is captured by an outsider (the "man in the center") and afterward adjusted to give distinctive public keys. Scrambled messages and reactions should likewise be blocked, decoded, and re-encoded by the assailant utilizing the right open keys for various correspondence portions, in all examples, to maintain a strategic distance from doubt.
Symmetric-key Cryptography
Symmetric-key calculations are calculations for cryptography that utilization similar cryptographic keys for both encryption of plaintext and decryption of ciphertext. The keys might be indistinguishable or there might be a straightforward change to go between the two keys. The keys, practically speaking, speak to a mutual mystery between at least two gatherings that can be utilized to keep up a private data interface. This prerequisite that the two players approach the mystery key is one of the principle downsides of symmetric key encryption, in contrast with public-key encryption (otherwise called asymmetric key encryption).
Symmetric-key calculations require both the sender and the beneficiary of a message to have a similar mystery key. All early cryptographic frameworks required one of those individuals to by one way or another get a duplicate of that mystery key over a truly secure channel.
Virtually all advanced cryptographic frameworks actually utilize symmetric-key calculations inside to scramble the heft of the messages, yet they take out the requirement for a genuinely secure channel by utilizing Diffie–Hellman key trade or some other public-key convention to safely come to concurrence on a new mystery key for each message (forward mystery).
At the point when utilized with asymmetric ciphers for key exchange, pseudo-random key generators are almost consistently used to produce the symmetric cipher meeting keys. Nonetheless, absence of arbitrariness in those generators or in their introduction vectors is tragic and has prompted cryptanalytic breaks previously. In this way, it is basic that an execution utilize a wellspring of high entropy for its introduction.
Examples of Symmetric Cryptography
Examples of popular symmetric-key algorithms include :
- Twofish
- AES
- DES
- 3DES
- Skipjack
Difference between Symmetric cryptography and Asymmetric cryptography
| Symmetric cryptography | Asymmetric cryptography |
|---|---|
| It only requires a single key for both encryption and decryption. | It requires two key one to encrypt and the other one to decrypt. |
| The size of cipher text is same or smaller than the original plain text. | The size of cipher text is same or larger than the original plain text. |
| In symmetric key encryption, resource utilization is low as compared to asymmetric key encryption | In asymmetric key encryption, resource utilization is high |
| Examples: 3DES, AES, DES and RC4 | Examples: Diffie-Hellman, ECC, El Gamal, DSA and RSA |
Block Ciphers
A block cipher is an encryption strategy that applies a deterministic calculation alongside a symmetric key to encode a block of text, instead of scrambling the slightest bit at a time as in stream ciphers. For instance, a typical block cipher, AES, scrambles 128 cycle blocks with a key of foreordained length: 128, 192, or 256 pieces. Block ciphers are pseudorandom stage (PRP) families that work on the fixed size block of pieces. PRPs are capacities that can't be separated from totally arbitrary changes and subsequently, are viewed as dependable, until demonstrated problematic.
Block cipher methods of activity have been created to take out the opportunity of encoding indistinguishable blocks of text a similar way, the ciphertext shaped from the past scrambled block is applied to the following block. A block of pieces called an instatement vector (IV) is likewise utilized by methods of activity to guarantee ciphertexts stay unmistakable in any event, when the equivalent plaintext message is scrambled various occasions.
Rules regarding Block Ciphers
Despite the fact that any size of block is adequate, following perspectives are borne as a top priority while choosing a size of a block.
-
Keep away from tiny block size − Say a block size is m bits. At that point the conceivable plaintext bits mixes are then 2m. In the event that the assailant finds the plain content blocks comparing to some recently sent ciphertext blocks, at that point the aggressor can dispatch a kind of 'word reference assault' by working up a word reference of plaintext/ciphertext sets sent utilizing that encryption key. A bigger block size makes assault more enthusiastically as the word reference should be bigger.
-
Try not to have enormous block size − With extremely huge block size, the cipher gets wasteful to work. Such plaintexts should be cushioned before being encoded.
-
Products of 8 digit − A favored block size is a numerous of 8 as it is simple for usage as most PC processor handle information in different of 8 pieces.
Examples of Block Ciphers
- Blowfish
- AES
- DES
- IDEA
Stream Ciphers
A Stream Cipher is utilized for symmetric key cryptography, or when a similar key is utilized to encode and decode information. Stream Ciphers encode pseudorandom groupings with pieces of plaintext so as to produce ciphertext, generally with XOR. A decent method to consider Stream Ciphers is to consider them creating one-time cushions from a given state.
It has two types:
1.Synchronous stream cipher
A Synchronous Stream Cipher creates a keystream dependent on inward states not identified with the plaintext or ciphertext. A paired added substance stream cipher is the term utilized for a stream cipher which XOR's the pieces with the pieces of the plaintext. Encryption and decryption require that the synchronus state cipher be in a similar state, in any case the message can't be decoded.
2.Self-synchronizing stream cipher
A Self-synchronizing Stream Cipher, otherwise called a nonconcurrent stream cipher or ciphertext autokey (CTAK), is a stream cipher which utilizes the past N digits so as to process the keystream utilized for the following N characters.
Difference between Stream and Block ciphers
| Stream Ciphers | Block Ciphers |
|---|---|
| Stream Cipher Converts the plain text into cipher text by taking 1 byte of plain text at a time. | Block Cipher Converts the plain text into cipher text by taking plain text’s block at a time. |
| Block cipher works on transposition techniques like Caesar cipher, polygram substitution cipher, etc. | While stream cipher works on substitution techniques like rail-fence technique, columnar transposition technique, etc. |
Conclusion
Hence , we arrive at the end of the article. Due to time and word constraints , I could not go further into defining the working of various examples of the ciphers, but I do hope that this article have given you a wide understanding of ciphers ,their use , working and types.
Hope this article is liked by you and I await positive criticism regarding the same.
Good Day!
