
Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
The Open Systems Interconnection (OSI) reference model is one of the most crucial networking concepts to comprehend. This conceptual model illustrates a network architecture that enables data to be transferred between computer systems.
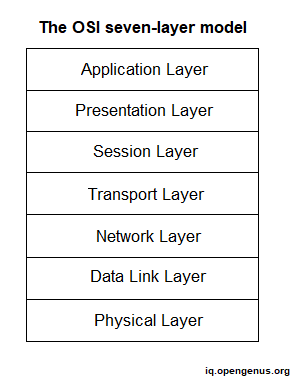
Each layer of the OSI model serves a distinct purpose. In this article, we will discuss about the functions of network layer and the protocols that are linked with it.
Table of contents:
- The Network Layer
- Protocols
- Network Layer Protocols
- Internet Protocol (IP)
- IPv4
- IPv6
- Internet Control Message Protocol (ICMP)
- Internet Group Message Protocol (IGMP)
- Address Resolution protocol (ARP)
- Reverse Address Resolution Protocol (RARP)
- Routing protocols
The Network Layer
The network layer's principal job is routing — providing ways for data to be sent from one network system to another. The network layer does not describe how data is transferred, but rather the techniques for doing so. Routing protocols, which are software components, offer functionality at the network layer.
Protocols at the network layer are also in charge of route selection, which is the process of finding the optimum path for data to travel across the network. In comparison to the DLL, which communicates on the LAN using MAC addresses, network layer protocols connect on the network using software-configured addresses and unique routing protocols. At the network layer, the term packet refers to the logical grouping of data.
Protocols
When computers were limited to isolated systems, there was minimal need for methods that allowed them to interact with one another. However, it wasn't long before the need to link computers in order to share data and printers became a must. More than a length of wiring was necessary to establish connection between network devices; a technique or set of rules was required to specify how systems would interact. That approach is provided by protocols.
It would be ideal if a single protocol allowed all devices to communicate with one another, however this is not the case. On a network, a variety of protocols can be employed, each with its own set of features, benefits, and drawbacks. The protocol you select can have a big influence on how the network operates and performs. This section delves into some of the most prevalent network layer protocols.
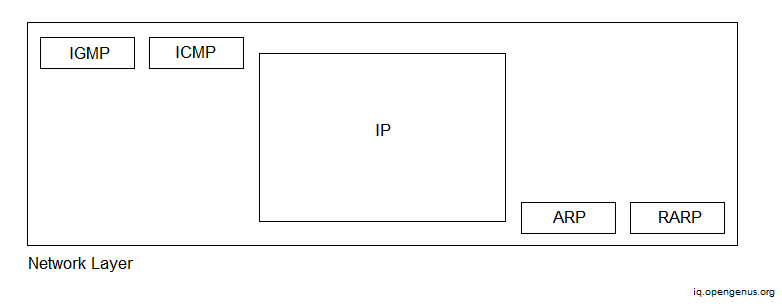
Network Layer Protocols
The network layer protocols are as follows:
- IP : primary protocol, in charge of best effort host-to-host transmission
- ARP : maps the next hop's IP address to its MAC/physical address (used for sending packets to the data-link layer)
- ICMP : Hosts and routers use this protocol to handle uncommon circumstances such as IP packet-header problems, inaccessible hosts and networks, and so on.
- IGMP : Hosts and routers employ it to perform efficient network-layer multi-casting.
- Routing protocols : is charge of routing table maintenance
Let us now discuss about these protocols in detail.
Internet Protocol (IP)
IP is a protocol that is used to transfer data from one network node to another. Because IP is connectionless, it cannot guarantee data transmission; it can only make best attempts to do so. A higher-level protocol, such as TCP, is necessary to ensure that IP communications are completed.
IP conducts fragmentation and reassembly operations for network communications in addition to offering best-effort delivery. Since the maximum transmission unit (MTU) size in IP is restricted, fragmentation is required. In other words, network messages that are too large to be sent in a single packet must be divided into smaller pieces and reassembled at the other end.
The IP can be divided into two versions:
IPv4
- IPv4 is the most widely used IP address.
- It is a 32-bit address.
- It is a four-field numeric address separated by a dot. For example, 63.76.10.35
- IPv4 has a restricted amount of IP addresses.
- It is compatible with VLSM (Virtual Length Subnet Mask). VLSM denotes that IPv4 converts IP addresses into subnets of varying sizes.
- IPv4 addresses are classified into five classes: Class A, Class B, Class C, Class D, and Class E.
- Security in IPv4 is determined by the application. This IP address was not created with the safety measure in mind.
- Senders and forwarding routers are responsible for fragmentation.
- It does not have a technique for identifying packet flows.
- It may be configured manually or using DHCP.
- It produces 4 billion distinct addresses.
- End-to-end connection integrity is not possible with IPv4.
- In IPv4, the checksum field is accessible.
- It doesn't support encryption or authentication.
- IPv4 is used for broadcasting.
IPv6
- IPv6 is the most recent version of IP.
- It is a 128-bit address.
- It is an alphanumeric address made up of eight fields separated by a colon. In IPv6, the representation of the IP address in hexadecimal.
- IPv6 has a high range of IP addresses.
- It does not support VLSM.
- Manual, DHCP, auto-configuration, and renumbering are all supported.
- It creates 340 undecillion distinct addresses.
- End-to-end connection integrity is possible with IPv6.
- IPSEC is a security protocol created for IPv6.
- Fragmentation is performed solely by senders.
- It identifies packet flows by using the flow label field in the header.
- In IPv6, the checksum field is not accessible.
- IPv6 uses multi-casting, which allows for more efficient network operations.
- It offers encryption as well as authentication.
Internet Control Message Protocol (ICMP)
This protocol describes a technique used by gateways and hosts to exchange control or error information. The Internet protocol offers unstable, connectionless datagram service, and a datagram travels from gateway to gateway until it reaches a gateway that can send it straight to its final destination. If a gateway is unable to route or deliver a datagram, or if it detects an unexpected circumstance, such as network congestion, that interferes with its ability to transmit the datagram, it must notify the original source to take action to prevent or fix the problem. The ICMP enables gateways to deliver error or control messages to other gateways or hosts; ICMP facilitates communication between Internet Protocol software on one system and Internet Protocol software on another.
This is a particularly unique message method that the designers incorporated into the TCP/IP protocols. This is to enable internet gateways to notify faults or offer information about unexpected occurrences. The IP protocol alone carries no information to assist the sender in testing connection or learning about errors.
ICMP simply transmits error conditions to the original source; the source should associate faults with specific application applications and take corrective action. It allows the gateway to notify the issue. It does not adequately describe the action to be performed in the event of a mistake. ICMP can only connect with the original source and not with intermediate sources.
ICMP messages traverse the internet in the data component of an IP datagram, which traverses the internet in the data portion of an IP datagram, which traverses each physical network in the data section of a frame. Datagrams containing ICMP messages are routed in the same way as datagrams carrying user information; there is no extra reliability or priority. If an IP datagram containing an ICMP message is not created for failures caused by datagrams holding ICMP error messages, an exception is issued to the error handling processes.
The ICMP messages are divided into two categories:
- Error Message : The error messages describe any issues that the hosts or routers may encounter when processing the IP packet.
- Query Message : The ICMP protocol may also be used to troubleshoot various network issues. Query messages allow hosts to obtain particular information from a router or from another host.
Internet Group Message Protocol (IGMP)
IGMP is also a protocol of the TCP/IP. The Internet Group Message Protocol (IGMP) is a protocol used on the Internet to manage multicast group membership on IP networks. Multicast routers are used to distribute packets to all hosts that are members of a certain group. These routers receive a large number of packets that need to be sent to various groups, but they are unable to broadcast them since it would raise the network's load. To address this issue, a list of groups and their members is kept, and IGMP assists the multicast router in doing so. The multicast router maintains a list of multicast addresses for which there are network members. Each group has a multicast router that delivers the group's multicast traffic to the members of that group.
The primary purposes of the IGMP protocol are to notify the local multicast router that the host want to receive multicast traffic from a specific group and to notify the local multicast router that the host wishes to exit a specific group.
Address Resolution protocol (ARP)
When a machine communicates with another machine on the same network, it needs to know its physical or MAC address. However, because the program has provided the destination's IP address, some technique is required to link the IP address to its MAC address. This is accomplished via the Address Resolution protocol (ARP). The destination node's IP address is broadcast, and the destination node tells the source of its MAC address.
However, this means that every time machine A wants to send packets to machine B, A must send an ARP packet to resolve B's MAC address, which increases traffic load significantly. To reduce communication costs, computers that use ARP keep a cache of recently acquired IP to MAC address bindings, so they do not have to use ARP repeatedly. Refinements to ARP ARP may be refined in several ways: When machine A wishes to transmit packets to machine B, it is probable that machine B will do so in the near future. So, to prevent ARP for machine B, A should include its IP to MAC address binding in the special packet that requests B's MAC address. Because A broadcasts its first request for B's MAC address, every computer on the network should extract and cache A's IP to MAC address binding. When a new computer joins the network (for example, when an operating system reboots), it can broadcast its IP to MAC address binding so that all other machines can cache it. This will avoid a large number of ARP packets sent by all other computers while attempting to interact with the new machine.
ARP's role is to resolve a system's IP address to the MAC address of the system's interface. ARP should not be confused with DNS or WINS, which also perform resolution duties but for different reasons.
Reverse Address Resolution Protocol (RARP)
Reverse Address Resolution Protocol (RARP) serves the same purpose as ARP, but in the other direction. To put it another way, it converts MAC addresses to IP addresses. RARP allows apps or systems to obtain their own IP address from a router or Domain Name System (DNS) server. Such a resolution is important for operations like executing reverse DNS lookups.
Cons of RARP:
- Because it functions at a low level, it requires direct network addresses, finding it challenging for an application programmer to design a server.
- Because the reply from the server carries just one little piece of information, the 32-bit internet address, it does not fully exploit the potential of a network like ethernet, which is obliged to deliver a minimum packet size.
Routing protocols
Routing is among the most fundamental aspects of networking that a network administrator must understand. Routing protocols govern how your data is routed and assist to make that process as seamless as feasible.
Routing protocols are necessary for a variety of reasons, including the following:
- Provides for the optimal path selection
- Enables loop-free routing
- Scales up to a very huge size
- Compatibility with current hosts and routers
- Variable length support
- Rapid convergence
- Reduces update traffic and is simple to set up
- Adapts to new situations
Network Routing Protocols are classified into two categories:
1. Static Routing Protocols : When an administrator manually allocates the path from the source network to the destination network, static routing protocols are employed. It strengthens the network's security.
2. Dynamic Routing Protocols : Dynamic routing protocols enable routers to automatically append information to their routing tables from linked routers. These protocols also transmit out topology updates anytime the network's topology changes.
Dynamic routing protocols can further be divided into two types:
I. Distance Vector Routing Protocol : Distance Vector Protocols use gobs of bandwidth and slow converge to publish their routing table to each and every directly linked neighbor at predefined time intervals. When a route becomes unavailable, all routing databases must be updated with new information.
II. Link State Routing Protocol : Link State Protocols provide a novel way to determining the optimum routing path. The route is computed in this protocol depending on the speed of the way to the destination and the cost of resources.
Protocols that assist data packets make their way over the Internet include the following:
- Routing Information Protocol (RIP)
- Interior Gateway Protocol (IGRP)
- Enhanced Interior Gateway Routing Protocol (EIGRP)
- Border Gateway Protocol (BGP)
- Open Shortest Path First (OSPF)
- Exterior Gateway Protocol (EGP)
- Intermediate System-to-Intermediate System (IS-IS)
Let's take a closer look at these protocols.
Routing Information Protocol (RIP) - RIP may be found in both LAN and WAN networks. It also operates on the OSI model's Application layer. There are two versions of RIP: RIPv1 and RIPv2. The RIPv1 assists you in determining network pathways based on the IP destination and hop count travel. RIPv1 also communicates with the network via broadcasting its IP table to all network-connected routers. RIPv2 is a little more advanced in that it forwards its routing table to a multicast address.
Interior Gateway Protocol (IGP) - IGRP is a distance-vector internal gateway protocol subclass. It is designed to circumvent RIP constraints. Load, bandwidth, latency, MTU, and dependability are the metrics employed. Routers commonly utilise it to share routing data inside an autonomous system. This routing system is ideal for bigger networks since it broadcasts every 90 seconds and has a peak hop count of 255. When contrasted to RIP, it aids in the maintenance of bigger networks. IGRP is also frequently used because it is immune to routing loops since it automatically updates itself when route changes occur inside the network. It also has the option of balancing traffic over equal or unequal metric cost pathways.
Enhanced Interior Gateway Routing Protocol (EIGRP) - EIGRP is a hybrid routing protocol that includes distance vector routing protocols, and link-state routing protocols. It uses the same composite metrics as IGRP to route the same protocols that IGRP does, assisting the network in selecting the optimum path destination.
Border Gateway Protocol (BGP) - When modifications are made, this routing protocol delivers updated router table data. As a result, there is no auto-discovery of topology changes, requiring the user to setup BGP manually.
Open Shortest Path First (OSPF) - The Open Shortest Path First (OSPF) protocol is a link-state IGP designed specifically for IP networks that use the Shortest Path First (SPF) approach. OSPF routing enables you to store databases containing information about the network's surrounding topology. It also employs the Dijkstra algorithm to rebuild network pathways when the topology of the network changes. This protocol is also particularly safe since it can validate protocol modifications to ensure data security.
Exterior Gateway Protocol (EGP) - EGP is a protocol for exchanging data between gateway sites that are neighbors inside autonomous systems. This routing protocol provides a platform for routers to exchange information between domains. The EGP protocol contains known routers, network addresses, route costs, and surrounding devices.
Intermediate System-to-Intermediate System (IS-IS) - On the Internet, the ISIS routing protocol is used to convey IP routing information. It is made up of several components such as end systems, intermediate systems, areas, and domains. The IS-IS protocol divides routers into groups known as regions. A domain is made up of several locations that are grouped together.
With this article, you must have the complete idea of different Network Layer Protocols.
