
Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
Passwordless login is useful in cases whereby we want to automate server administration tasks. We discuss how to configure ssh passwordless login in Linux.
Table of contents.
- Introduction.
- Requirements.
- Setup.
- Configuring passwordless login.
- Disabling passwordless login.
- Summary.
- References.
Introduction.
Secure Shell(SSH) is a cryptographic networking protocol we use for encrypting communications between computers over the internet.
For use to use ssh we require authentication and the two authentication methods are password-based authentication which we have seen here and public key-based authentication.
A public key is shared while the private is only known by the owner. For the connection to be established, the certificate is checked then a session is generated that encrypts with the public key and the other end decrypts it with a private key.
Requirements.
The following are requirements for this to work.
- Both hosts must be on and connected to the internet and be reachable
- Permissions and authentication details for the user account on the remote server.
- A SSH client should be installed on the client's computer.
- A SSH server should be installed on the server.
- Firewall rules allowing the ssh connection on the server.
Setup.
We have two hosts,
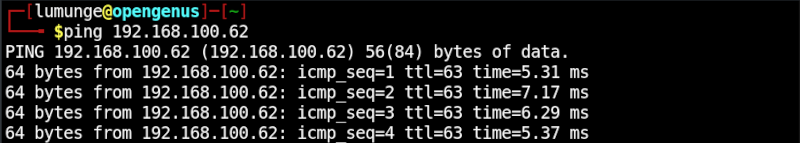
The server IP address is 192.168.100.62 and the client's IP address is 192.168.100.62
We make sure that it is reachable by sending ICMP packets.
On localhost
$ ping 192.168.100.62
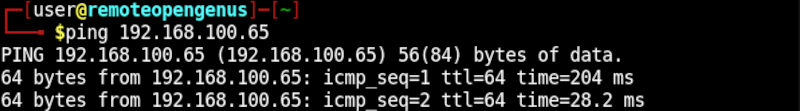
On the remote host:
$ ping 192.168.100.65
Configuring passwordless login.
In this section, we go over the steps taken to set up passwordless login to a remote server.
1. Existing keys.
Before we start we first check for existing keys in the .ssh directory located in the home directory:
$ ls ~/.ssh
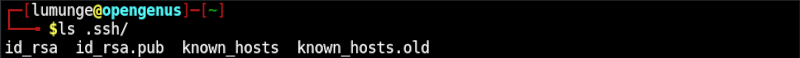
If keys exist, it is wise to back them up to avoid issues later.
2. Key generation.
Next, we have to generate a public key on our local host machine. For this we use the ssh-keygen command as follows:
$ ssh-keygen -t rsa
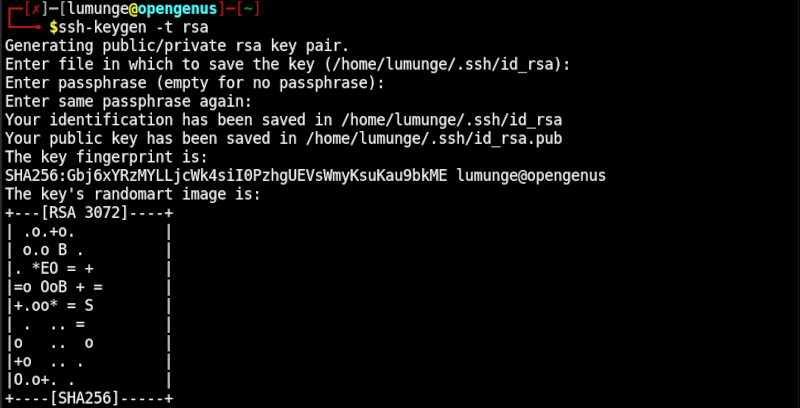
Above, we press the enter key until the key is generated.
Notice that we have used the rsa encryption algorithm, we can also use a different algorithm such as dsa. We can also specify the number of bits, for example, to specify a 4096-bit key we write:
$ ssh-keygen -t rsa -b 4096
3. Copying key to the remote server.
Next, we copy the generated public key to the remote server using the ssh-copy-id command as follows:
$ ssh-copy-id [username]@[hostname/IP]
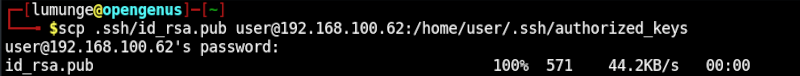
We can also use SCP to copy the public key to the remote server as follows:
$ scp [public key path] [username]@[hostname/IP]:[remote file path]
4. Configuring permissions.
Before we can connect to the remote server via ssh we have to change file permissions of the .ssh directory and .ssh/authorized_keys file.
We change permissions as follows:
$ ssh [username]@[hostname/IP] "chmod 700 .ssh; chmod 640 .ssh/authorized_keys"
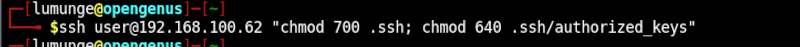
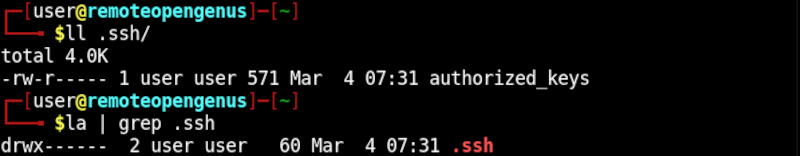
The permissions should look like the following:
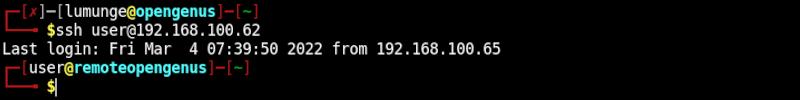
5. Log in to the remote server.
If successful we should not be prompted for a password when we log in to the remote server.
$ ssh user@192.168.100.62
Disabling passwordless login.
We can disable passwordless login to the remote server by editing the ssh configuration file as follows:
$ vim /etc/ssh/ssh_config
We paste the following in the file:
PermitRootLogin no
PubkeyAuthentication yes
PasswordAuthentication no
UsePAM yes
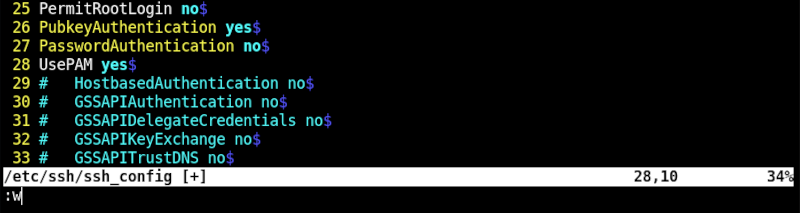
Once this is done we save the file and restart the ssh service as follows, so the changes can take effect:
$ sudo systemctl restart ssh
Summary.
Passwordless login is useful in cases whereby we want to automate tasks such as backups, file synchronization, etc.
In this article at OpenGenus, we have seen how to configure passwordless login when using ssh in Linux.
References.
For the ssh manual page we execute the command, $ man ssh.
