Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
Reading time: 10 minutes
Tabnabbing is a form of cyber attack which enables an hacker to take the advantage of the idle tabs in the browser and use them for carrying out the phishing attacks. The attack can be carried out even if the javascript is disabled, using the HTML attribute or a "meta refresh" meta element which are used for page redirection that causes a reload of a specified new page after a period of time. Also, the attack causes the browser to navigate to the spoofed page after the page has been left idle for some time.
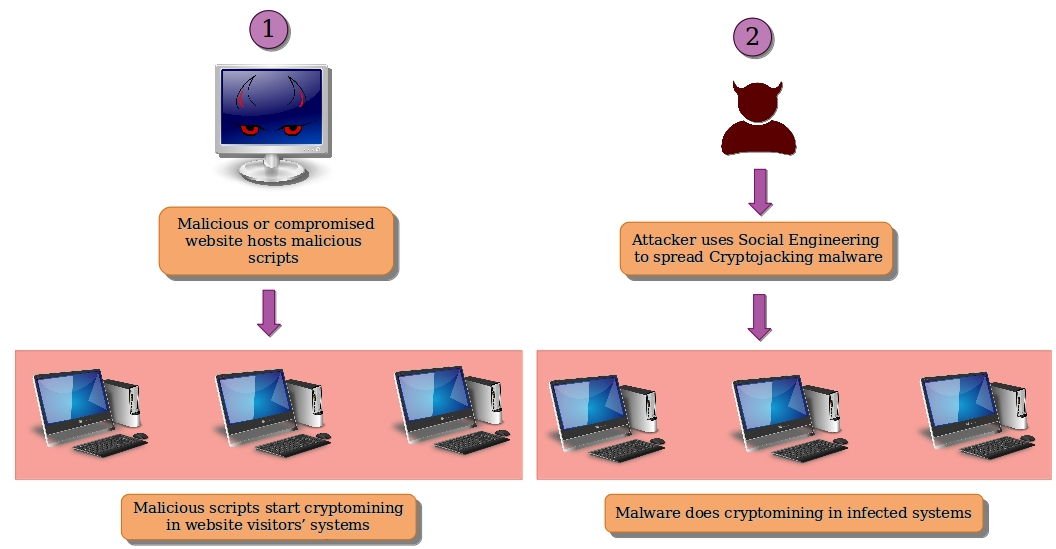
Procedure For The Attack
- The hacker first creates a malicious website which have malicious script running in the background of website which are capable of detecting all the other tabs open in the current browser, and check if it those tabs are idle and inactive.
- When a user opens that malicious website, the script starts to execute. If any other tab is found idle and inactive, then the malicious script executes itself and rewrites the whole webpage in the tab where the malicious site was opened.
- To evade any type of detection, the malicious script even changes the title of the webpage along with favicon of the site. When the user comes back, he sees the malicious webpage as a genuine page (for example, a Gmail login page) asking for credentials. If the user provides his credentials, the information is sent directly to the hacker.
Image For Understanding The Attack
Mitigation For The Attack
Make sure that the website uses HTTPs and proper digital certificates. Always check the URL before entering the credential. Do not allow scripts on a webpage if the site is not trusted.