Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
Reading time: 6 minutes
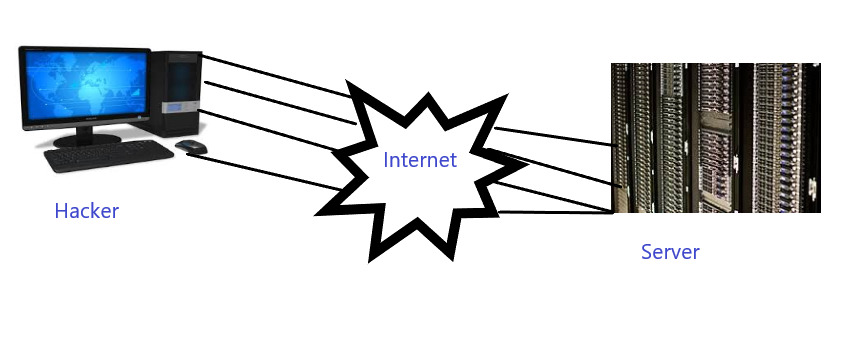
UDP Flood Attack is a type of Denial of Service attack in which a hacker floods the random ports on the victim host with UDP packets. The attack enables the hacker to perform the attack anonymously. In this attack, the hacker spoofs the IP Address of the packets, to make sure that the returning ICMP packets don’t reach back to the hacker.
Procedure For The Attack
- UDP is a connectionless and sessionless protocol and therefore doesn’t require a three-way handshake like TCP. Hackers exploit this vulnerability to send a high volume of garbage-filled UDP packets to any of the host.
- When the victim host receives the garbage-filled UDP packets, it checks for the application listening on that port.
- When the host sees that no associated application is listening, it replies with an ICMP Destination Unreachable packet, further amplifying the network flood.
Image For Understanding The Attack
Mitigation For The Attack
Check and drop the UDP traffic which is not related to DNS at the network edge. Limit the rate of the ICMP responses to prevent this type of attack and also filter out or block the malicious UDP packets through an updated firewall.
MCQ
Question 1
UDP Flood is an type of which attack?
Phishing Attack
Spoofing Attack
DoS Attack
MitM Attack
Question 2
UDP doesn't require what?
Three Way Handshake
Two Way Handshake
One Way Handshake
Four Way Handshake