Open-Source Internship opportunity by OpenGenus for programmers. Apply now.
Reading time: 14 minutes
Denial Of Service Attack is a form of cyber attack basically used by hackers to prevent the victims from accessing any legitimate service. This hacker floods the web servers with excessive traffic in order to succeed in this attack. The attack does not result in theft or loss of data but can cause victim a great deal of time and money to handle this type of attack.
Procedure For The Attack
Attack Procedure is as follows:
-
A hacker first searches for the target on which he wants to attack. For example, www.shop.com is a website where he wants to attack.
-
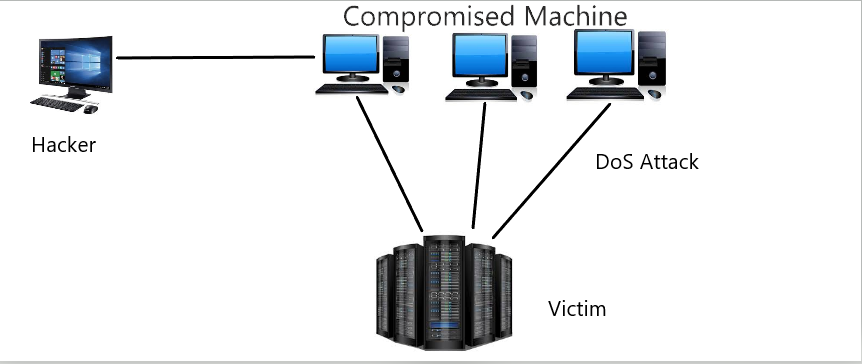
After finding the target, the hacker first spreads the malware to various systems through spam emails or various methods of social engineering and compromise those systems to behave as bots.
-
After compromising the system, now the hacker targets the victim and for this he will use all the compromised systems traffic to redirect to the victim website, for example, if www.shop.com cannot handle more than 1000 requests in a minute, so a hacker, therefore, sent excessive messages to flood the website with extra traffic that the victim web servers cannot handle in a minute.
-
If the website is not opening or is showing an error on the webpage that means the attack is successful. i.e. www.shop.com is inaccessible and anyone cannot access the website for a while until the systems are restored and get back to the operational mode.
Mitigation For The Attack
Restrict the number of requests a server can accept over a specified time window is a way of preventing the denial-of-service attacks. The WAF(Web Application Firewall) can also help to avoid this kind of attack. Organizations should have a modern and up-to-date security infrastructure for handling this type of attack. Update the anti-malware software and firewalls time to time.